
When the conversation about email signature software starts, it usually begins with design.
Someone shows a mockup, talks about brand colors, and asks if you can add a promotional banner. And while those are all reasonable topics to bring up, they’re not the ones that determine whether or not a tool will actually work for your organization.
Unfortunately, IT considerations tend to surface later, often after a tool has already been purchased by a non-technical team… and then someone realizes it doesn’t integrate with your directory, or that it stores data in a region that conflicts with your data residency requirements.
So to help you avoid any costly implementation issues, we’re covering the five factors IT teams should evaluate when choosing an email signature solution, along with the essential questions to ask every vendor before you commit.
Why Early IT Involvement Matters
Email signature management touches more of your IT infrastructure than it appears to at first glance.
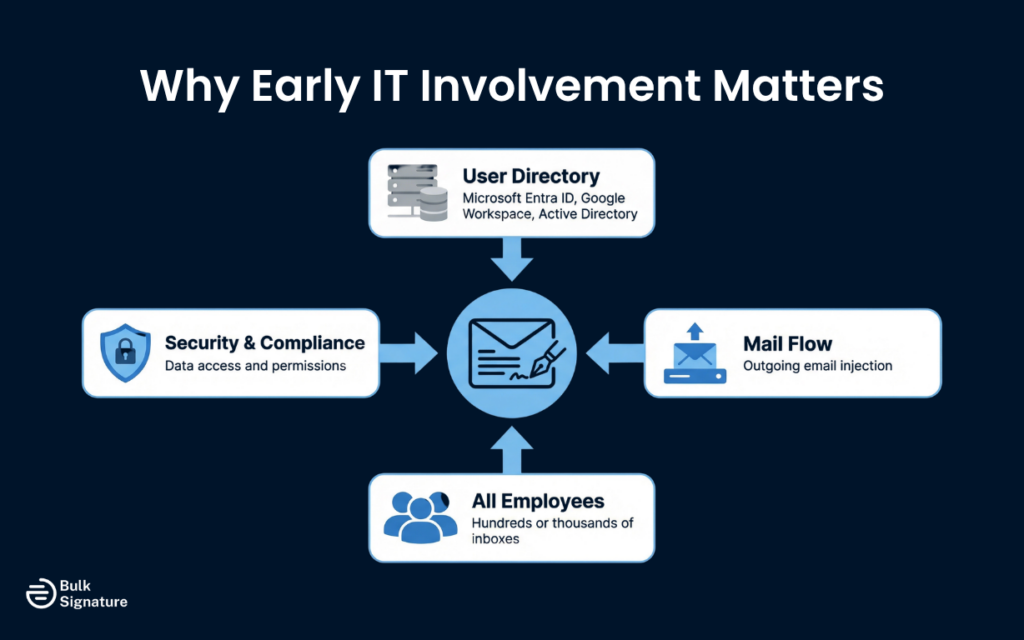
A signature tool needs to know who your employees are, what their job titles are, and which department they belong to. That means it needs access to your user directory. It also needs to inject signatures into outgoing emails, which means it needs to sit somewhere in your mail flow. And, it needs to handle signature updates across potentially hundreds or thousands of inboxes, which means it needs a deployment mechanism that doesn’t rely on individual users having to do anything.
Get any of these integrations wrong, and you’ll end up with a tool that either doesn’t work reliably or one that solves some problems while also creating new ones.
More on why this can get so messy without the right tool here: The Hidden Cost of Manual Email Signature Management (Why You Need a Tool)
What IT Teams Need to Check Before Signing Off On Email Signature Software
Most email signature solutions will have all the basic features for marketing and non-technical users, like a template library, promotional banners, and campaign scheduling. However, that doesn’t mean they’ll meet the demands of your actual IT environment.
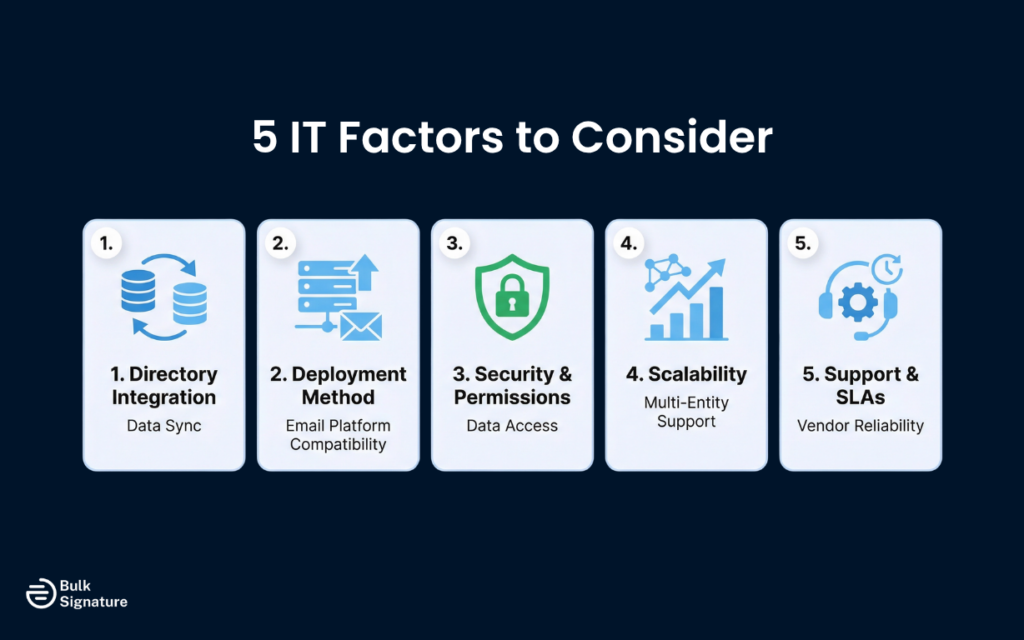
Below are five critical IT factors to consider, based on where organizations most often encounter the most trouble during implementation. By addressing these early on, you’ll be well-positioned to choose an email signature solution that will work reliably for your entire organization at scale.
Factor 1: Directory Integration and Data Sync
The most practical benefit of centralized email signature management is that signatures can be populated automatically from your user directory. So instead of asking employees to type their own name, title, and phone number, the tool pulls that data directly from your directory and inserts it into the correct fields.
But this only works if the tool integrates with the directory you’re actually using.
The most common directories in enterprise environments are Microsoft Entra ID, Google Workspace, and on-premises Active Directory. Some organizations use a combination of these, especially if they’ve migrated partially to the cloud or operate across multiple entities.
What happens when an organization runs both Entra ID and on-premises AD simultaneously?
In a hybrid identity setup, user data is typically synchronized from Active Directory to Microsoft Entra ID using tools like Azure AD Connect or Azure AD Connect Cloud Sync. On paper, this creates a unified directory. But for email signatures, it often creates a dependency on partially synchronized data that may not reflect real-time or complete user information, leading to different formats, missing fields, or outdated information appearing in live email conversations.
To avoid signature inconsistencies, you need a way to manage user data centrally rather than depending on how different directories happen to sync.
A practical way to approach this is to break the migration into the following structured phases:
Hybrid Directory Migration Plan for Reliable Email Signature Data
Phase | What IT Teams Should Do | Why It Matters for Email Signatures |
1. Define source of truth | Assign ownership of attributes (such as HR via Workday for titles, or IT directories for contact data) | Prevents conflicting data from appearing in signatures |
2. Normalize attributes | Align field names and formats across Active Directory and Microsoft Entra ID | Enables consistent signature rendering across all users |
3. Optimize sync layer | Audit and manage Azure AD Connect or Azure AD Connect Cloud Sync | Reduces delays and prevents outdated signature data |
4. Introduce directory-agnostic signature platform | Implement a solution like BulkSignature | Maintains consistency even when directories are still evolving |
5. Migrate in phases | Move users in controlled batches and validate data accuracy at each step | Limits risk of broken or incomplete signatures during transition |
6. Validate before decommissioning AD | Confirm all users and attributes are fully cloud-managed before retiring on-prem systems | Avoids last-minute data gaps that disrupt signatures |
In addition to aligning your directory data, it’s also important to understand how data actually moves and updates between systems. This includes whether updates happen in real time or on a schedule, and how quickly changes (such as a new job title) are reflected in user signatures. For organizations with more complex structures, it’s also worth checking if the tool can pull data from multiple directories simultaneously, rather than relying on a single source.
Directory integration is one of the areas where the difference between tools becomes most apparent. Some platforms offer deep, configurable sync with support for custom attributes. Others offer a basic connection that works well for simple signature structures but struggles with anything more complex. That’s why it’s important to validate how well the integration handles your specific environment before committing.
Factor 2: Deployment Method and Email Platform Compatibility
There are two fundamentally different ways that email signature software can apply signatures to outgoing emails: client-side and server-side.
Client-side tools modify signatures at the point of sending, either through a browser extension, a desktop application, or a plugin installed in the email client. Server-side tools intercept outgoing emails at the mail server level and apply the signature before the message reaches the recipient.
Each approach has different implications for IT.
Client-side deployment requires something to be installed or configured on each user’s device. That means a rollout process, ongoing maintenance, and the possibility that signatures won’t be applied if a user is on an unmanaged device or hasn’t installed the required extension. It also means that users can potentially modify or remove the signature if they have access to the settings.
Common Pitfalls of Client-Side Deployment: Signatures fail silently on unmanaged devices, users on mobile send without signatures, and extension updates break functionality across the fleet.
Server-side deployment removes the dependency on individual devices entirely. Signatures are applied centrally, regardless of what device or client the user is sending from. This is generally more reliable for organizations that need consistent signatures across a large workforce, but it requires the tool to be integrated into your mail flow, which has its own configuration requirements.
Common Pitfalls of Server-Side Deployment: Misconfigured mail flow rules cause double signatures or stripped formatting, delays in the transport pipeline, and complications with encrypted or S/MIME messages.
The right choice depends on your email platform and your organization’s technical setup. The table below summarizes the key differences:
Email Signature Deployment Methods Compared
Deployment Method | How It Works | Best For | Key Consideration |
Client-side (plugin/extension) | Installed on each user’s device or email client | Small teams with managed devices | Requires rollout and maintenance per device |
Server-side (mail flow) | Integrated at the mail server or gateway level | Larger organizations needing centralized control | Requires mail flow configuration and testing |
Cloud-based (API integration) | Connects via API to your email platform (e.g. Microsoft 365, Google Workspace) | Cloud-first organizations | Dependent on API permissions and rate limits |
For organizations using Microsoft 365 or Google Workspace, cloud-based API integration is increasingly common. It avoids the need for local installation while still applying signatures centrally.
Common Pitfalls of API-Based Integration: Rate limits during bulk sends, token expiry causing outages, and permission scope changes after a platform update.
It’s also worth noting that API-based deployment requires the signature platform to be granted controlled access to your email environment. This typically involves tenant-level or domain-wide permissions, which should be carefully reviewed from a security vulnerabilities and compliance standpoint before approval.
The following table outlines what this access typically looks like across major platforms:
API-Based Email Signature Integration: Permissions Overview
Platform | Typical Permissions / Access | What It Enables | Security Consideration |
Microsoft 365 | Mail.ReadWrite, User.Read.All + tenant-wide admin consent | Apply signatures to outgoing employee emails and map signatures to user profiles across the organization | Broad organizational access; requires careful admin consent and vendor trust |
Google Workspace | OAuth scopes + domain-wide delegation | Act on behalf of users to apply signatures consistently across all accounts | Domain-wide delegation increases scope; requires strict control of granted permissions |
BulkSignature is designed with a least-privilege, security-first model. The platform only requests the minimum permissions required to apply and manage signatures centrally, with clear justification for each scope.
You can learn more about BulkSignature’s data access and permissions for Google Workspace and Microsoft 365 in our privacy policy.
Factor 3: Security, Permissions, and Data Access
Any tool that integrates with your email infrastructure and user directory will require access to sensitive data. Understanding exactly what access is required, and what the tool does with that data, is a non-negotiable part of the evaluation process.
The best place to start is with the permissions model. What level of access does the tool need to your Microsoft 365 or Google Workspace environment? Does it require admin-level permissions, or can it operate with more limited access? Can permissions be scoped to specific functions, or does the tool require broad access to your entire tenant?
Then consider data storage. Does the tool store copies of your employee data, including names, job titles, and contact details? If so, where is that data stored, and for how long? This is particularly relevant for organizations with data residency requirements, where employee data may need to remain within a specific geographic region.
In addition to core permissions and data handling, it’s important to look at the platform’s broader security capabilities. This includes support for single sign-on (SSO) via SAML or OAuth, as well as multi-factor authentication to protect access to the admin console.
You should also confirm whether the tool provides a detailed audit log of changes made to signatures, templates, and user assignments. On the vendor side, review how security incidents are handled, including their notification timelines, and whether the platform has undergone third-party security testing or holds certifications such as ISO 27001 or SOC 2.
These aren’t questions that vendors should find unusual. A reputable tool will have clear answers to all of them. Vague responses or deflection on any of these points is worth treating as a red flag.
Factor 4: Scalability and Multi-Tenant or Multi-Entity Support
Email signature software requirements change as organizations grow. A tool that works well for 50 employees may not scale effectively to 500, and a tool designed for a single entity may not support the structure of an organization with multiple subsidiaries or regional offices.
Think about your organization’s structure and how it’s likely to evolve over the next two to three years.
If you operate across multiple legal entities, you may need the ability to manage separate signature templates for each entity, with different branding, different disclaimers, and different default settings. Some tools handle this through a multi-tenant model, where each entity has its own isolated environment. Others handle it through a permission-based structure within a single account, where different administrators can manage specific groups of users.
If you’re in a period of growth, consider how the tool handles onboarding at scale. When a new employee joins, how quickly does their signature get provisioned? Is it automatic, or does it require manual updates from an administrator? For organizations hiring in volume, the difference between automatic provisioning and a manual signature process can represent a meaningful operational overhead.
It’s also worth considering how the tool handles role-based access. IT may need full administrative access, marketing may only need the ability to update campaign banners, and HR may need read-only visibility for compliance purposes. A well-designed tool will support granular permission levels that reflect these different needs.
Factor 5: Support, SLAs, and Vendor Reliability
Email is a critical communication channel. If your signature tool goes down, or if a misconfiguration causes signatures to stop being applied, the impact is immediate and visible to everyone your organization communicates with.
That’s why, when evaluating the best email signature software for your organization, it’s important to look beyond the feature list and assess the operational side of the vendor relationship.
Start by reviewing the vendor’s reliability. This includes their uptime history, whether they provide a public status page, and the terms of their SLA for resolving critical incidents, along with any remedies if those commitments aren’t met.
Next, consider their support model. Look at whether support is available during your business hours, whether it’s handled by a dedicated team or a shared inbox, and whether enterprise customers are assigned an account manager.
Finally, evaluate the implementation process. Some vendors offer hands-on technical onboarding, while others rely primarily on documentation. For organizations with more complex directory structures or mail flow configurations, direct implementation support can make a significant difference to how smoothly the rollout goes.
It’s also worth asking about their product roadmap and release cadence. Email platforms like Microsoft 365 and Google Workspace update regularly, and a signature tool that doesn’t keep pace with those changes can quickly become unreliable. On the other hand, a vendor that communicates openly about upcoming changes and maintains a responsive development cycle is a more reliable long-term partner than one that ships infrequently and is slow to address cross-platform compatibility issues.
Putting It All Together: A Pre-Purchase Email Signature Manager Checklist for IT
Before committing to any software for managing email signatures, it’s worth working through the following questions with the vendor:
Choosing Email Signature Solution: Key Questions to Ask
IT Evaluation Area | Questions to Ask Each Vendor | Why It Matters |
Directory integration | Which directories do you support?
How does sync work, and how frequently does it update? If the answer is “every 24 hours,” ask what happens to a signature during that window after a user’s title changes (Real-time sync via webhooks is stronger than scheduled polling.) | Keeps user data accurate and up to date without relying on manual input. |
Deployment method | Is this client-side, server-side, or API-based? What are the infrastructure requirements? | Affects rollout complexity, reliability, and how consistently email signatures are applied. |
Security and permissions | What access does the tool require? Where is employee data stored? What certifications do you hold? A good answer names SOC 2 Type II or ISO 27001 with a link to the actual report, not just a mention. Type I is weaker than Type II. Vague references to “enterprise-grade security features” with no documentation are a red flag. | Impacts data protection, compliance posture, and overall risk exposure. |
Scalability | How does the tool handle multiple entities or subsidiaries? What does the permission model look like? | Supports growth and avoids added administrative overhead as the organization expands. |
Support and reliability | What is your uptime SLA? What does your support model look like? How do you handle critical incidents? | Influences business continuity and how quickly issues are resolved. |
Working through these questions before you begin a trial or proof of concept will not only save your team a ton of time, but it will reduce the risk of discovering a fundamental incompatibility after you’ve already invested in the evaluation process.
Not sure if you’ve covered everything? Read this: The IT Buyer’s Final Checklist for Company-Wide Email Signature Management
Making the Right Call for Your Organization
Choosing a professional email signature solution involves multiple stakeholders, each with different priorities:
- Marketing teams want complete control of brand consistency.
- Legal teams want to ensure compliance.
- HR teams want consistent email signatures with up-to-date employee details.
- Finance teams want to understand the cost model.
And IT? IT has to make all of it work reliably, securely, and within the constraints of your existing infrastructure.
The five factors above are where (in our experience) IT’s perspective tends to surface requirements that other teams may not have even considered yet, like permission scopes or mail flow dependencies. By bringing these into the conversation early, before a vendor is selected, IT has a chance to shape the decision, rather than being left to deal with the consequences later.
If you’re actively looking for a reliable, scalable email signature solution, BulkSignature was specifically built for IT and operations teams managing signatures at scale, with support for Microsoft 365 and Google Workspace, centralized management for templates, and granular permission controls.
Finding the Right Email Signature Tool: How BulkSignature Meets IT Requirements
IT Requirement | Why It Matters | BulkSignature |
Directory Integration | Keeps signatures accurate and automatically updated | Supports Microsoft Entra ID, Google Workspace, and on-premises Active Directory with real-time sync via webhooks |
Flexible Deployment | Works reliably across all users and devices | Further information on deployment |
Security & Compliance | Protects sensitive data and meets compliance needs | Further information on security and compliance |
Scalable Management | Handles growth, multiple entities, and permissions | Further information on access and permissions |
Reliable Support | Keeps email communication running without disruption | Contact us anytime! |
If you’d like to see how BulkSignature meets all 5 factors in this article, book a free demo and take a look at our transparent pricing to see what you’ll get before you commit.
Frequently Asked Questions About Choosing an Email Signature Solution
What is the difference between client-side and server-side email signature deployment?
Client-side deployment requires a plugin, extension, or application to be installed on each user’s device, and the signature is applied at the point of sending from the user’s machine.
Server-side deployment applies signatures centrally at the mail server or gateway level, meaning signatures are added regardless of which device or client the user sends from.
Server-side approaches are generally more reliable for large organizations, but they require integration with your mail flow infrastructure.
Does email signature software need admin access to Microsoft 365 or Google Workspace?
Most tools require some level of elevated permissions to integrate with your email platform and user directory. The specific permissions required vary by tool and deployment method.
In Microsoft 365, there are two main models:
- Delegated permissions: act on behalf of a signed-in user (more limited scope)
- Application permissions: run independently with organization-wide access (higher risk, typically requires tenant-level admin consent)
Some tools require Global Admin approval, while others can operate with Exchange Admin roles or custom-scoped permissions. Tools using broad application permissions generally carry a wider access footprint than those using scoped delegated access.
BulkSignature requires Global Admin access during initial setup to establish secure integration, but roles can be adjusted, and different users can be invited with appropriate permission levels after installation.
How do I evaluate whether an email signature management solution will scale with our organization?
Look at how the tool handles multi-entity structures, role-based access controls, and automated provisioning for new users. Ask the vendor for case studies or references from organizations of a similar size and complexity to your own. It’s also worth asking how the tool has handled growth for existing customers, and if there are any known limitations at higher user volumes.
Can email signature software apply different signatures to different departments or roles?
Yes, most enterprise-grade tools support conditional logic that applies different email signature templates based on attributes like department, job title, location, or seniority. This allows you to maintain a consistent brand framework while accommodating legitimate differences in signature content across your organization.
What other factors should we consider when choosing an organization-wide email signature solution?
Beyond deployment and permissions, several practical factors influence long-term success:
- Brand consistency and brand recognition: Support for key brand identity elements, like company logos, colors, fonts, and social media icons.
- Legal compliance: Ability to include and manage legal disclaimers across regions or departments.
- Marketing features: Built-in support for marketing banners, campaigns, Google Analytics, and trackable links.
- Personalization: Dynamic fields for creating personalized signatures, such as names, titles, contact details, and social media profiles.
- Mobile compatibility: Signatures that render correctly across mobile devices and email clients.
- Scalability: Ability to manage updates across large or distributed teams without manual work.
- Support: Availability of onboarding guidance and dedicated account management for large teams.
The most effective solutions balance central control with flexibility, allowing different teams to meet their goals without compromising consistency or security.





