Deploying email signatures across an entire organization is one of those tasks that sounds simple but quickly turns into an operational headache. This guide covers every method available in 2026 to deploy email signatures organization-wide — from native Google Workspace and Microsoft 365 tools to third-party platforms — with step-by-step instructions, limitations, and the trade-offs IT teams need to know.
Quick Answer: To deploy email signatures organization-wide, you have three main approaches. In Google Workspace, use the Append Footer setting for basic text disclaimers or the Gmail API for HTML per-user signatures. In Microsoft 365, use Exchange Online transport rules for server-side disclaimers (limited formatting, no Sent Items visibility). For full control — branded HTML designs, department-based targeting, dynamic fields, and coverage across all email clients — use a third-party signature management platform like BulkSignature that syncs with your directory and deploys centrally.
Quick Start Checklist to Deploy Email Signatures Organization-Wide
Standardizing email signatures sounds simple until you try to deploy email signatures organization-wide for 50, 500, or 5,000 users. What starts as a branding request quickly turns into an operational problem: inconsistent signatures, missing legal disclaimers, broken images, VIP exceptions, onboarding gaps, and endless tickets from users who changed just one line.
For IT teams, email signatures are less about design and more about governance, automation, and supportability. Both Google Workspace and Microsoft 365 offer native ways to enforce some form of organization-wide signature behavior — but their native approaches behave differently, and neither platform fully solves every deployment scenario on its own. That is why IT admins typically choose between native controls, Windows-based workarounds such as Group Policy, or a dedicated signature management platform.
This guide walks you through each approach to deploy email signatures organization-wide, step by step, so you can choose the right deployment model for your environment and roll it out without the usual headaches.
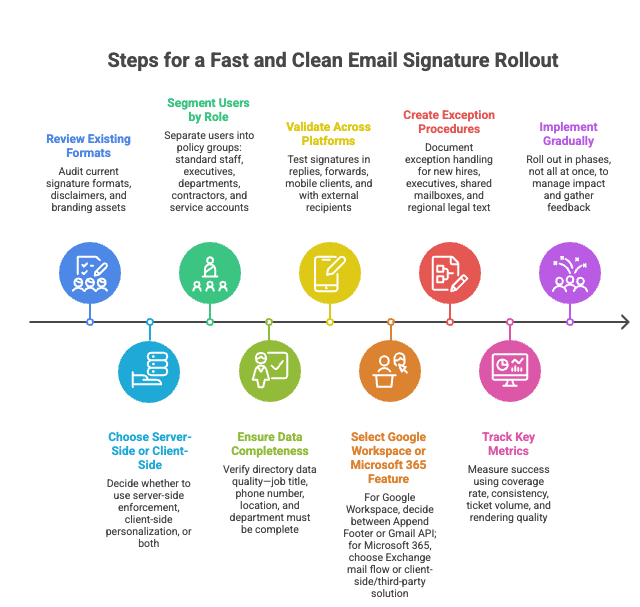
If you need to move fast, this is the shortest path to a clean rollout:
- Audit your current signature formats, disclaimers, and branding assets.
- Decide whether you need server-side enforcement, client-side personalization, or both.
- Separate users into policy groups: standard staff, executives, departments, contractors, and service accounts.
- Verify your directory data quality — job title, phone number, location, and department must be complete.
- Test signatures in replies, forwards, mobile clients, and with external recipients.
- For Google Workspace: decide whether the Append Footer feature is enough or whether you need Gmail API-based per-user signatures.
- For Microsoft 365: decide whether Exchange mail flow disclaimers are acceptable or whether you need a client-side or third-party solution.
- Document exception handling for new ires, executives, shared mailboxes, and regional legal text.
- Measure success using coverage rate, consistency, ticket volume, and rendering quality.
- Roll out in phases, not all at once.
Why Manual Signature Deployment Breaks at Scale
At small scale, asking users to paste a signature into Gmail or Outlook seems harmless. At organizational scale, it creates four predictable problems.
First, users modify templates. Even if you send an approved signature block, people shorten job titles, remove legal text, paste low-resolution logos, or add personal quotes. Second, signatures drift over time. New phone numbers, rebrands, acquired business units, and office moves do not propagate cleanly when every user manages their own footer.
Third, IT ends up doing repetitive support work: fixing image hosting, troubleshooting formatting, and rebuilding signatures after profile resets or device migrations. A 500-person company updating signatures quarterly spends an estimated 125 hours per year on manual changes alone.
Fourth, manual signatures create compliance blind spots because there is no guarantee that required legal text appears on every outgoing message.
This is why mature deployments treat signatures like any other configuration standard. When you deploy email signatures organization-wide, the goal is not merely to have a nice footer, but to ensure consistency, automate personalization, and reduce dependency on end users.
Deployment Models to Deploy Email Signatures Organization-Wide
Before touching any settings, decide which operating model you need. This decision shapes everything that follows when you deploy email signatures organization-wide.
Server-side deployment appends or prepends content after the message leaves the user. It is strong for compliance and guaranteed coverage, but weaker for user visibility during compose. In Microsoft 365, this is done with Exchange mail flow disclaimer rules. In Google Workspace, this is the appended footer feature.
Client-side deployment places the signature directly into the compose window so the sender sees it while writing. This is better for polished formatting and user experience, but harder to control across devices and clients unless you automate it carefully. In Google Workspace, the Gmail API can programmatically update user signatures. In Microsoft environments, classic Outlook historically relied on local files and profile-level settings, which is why admins often used scripts, GPOs, or add-ins.
The right answer depends on your priorities. If legal text must never be omitted, server-side enforcement matters most. If sales and leadership care about branded layouts, banners, and polished replies, you need more than native server-side rules alone.
Deploy Email Signatures Organization-Wide: Method Comparison
Here is a side-by-side view of all four common approaches to deploy email signatures organization-wide:
| Approach | Best Use Case | Design Flexibility | Mobile Support | Maintenance |
|---|---|---|---|---|
| Google Append Footer / Exchange Disclaimer | Mandatory legal text, simple standardization | Limited (plain text or basic HTML) | Yes (server-side) | Medium |
| Gmail API / Custom Scripting | Google Workspace personalization at scale | High (full HTML) | Yes (server-side) | High — requires engineering |
| Group Policy / Login Scripts | Classic Windows + Outlook desktop environments | High (full HTML) | No — desktop only | High — per-device deployment |
| Third-Party Signature Platform | Cross-platform branding, campaigns, delegation | High (visual editor) | Yes (server-side) | Low — centralized dashboard |
How to Deploy Email Signatures in Google Workspace
If you use Google Workspace and need to deploy email signatures organization-wide, Google gives admins two main paths: a centrally appended footer and programmable user signatures.
Option 1: Use the Gmail Append Footer Setting
In the Google Admin Console, admins can go to Apps > Google Workspace > Gmail > Compliance and configure the Append Footer setting. This applies a standard text footer to outbound mail, and optionally to internal messages as well. By default, the footer is only added to mail sent outside the organization. Users cannot edit or remove the appended content, making it useful for legal or mandatory corporate text.
Implementation note: changes can take up to 24 hours to propagate across your organization, although they often apply sooner.
This method is best when your priority is enforcement rather than personalization. It works well for legal language, confidentiality notices, and a simple company-wide sign-off. It is less ideal if you want every user to have a fully personalized block with their title, phone number, banners, and role-specific content visible while composing.
Option 2: Manage Per-User Signatures Through the Gmail API
The Gmail API supports managing signatures through the settings.sendAs resource. In practice, you can update signatures programmatically per user or per alias. This gives IT far more control than asking users to configure signatures manually, and the signature appears in the compose window rather than being invisibly appended after send.
This is the better fit for personalized signatures at scale. The tradeoff is operational complexity: you need a script, a service account strategy, and a maintenance plan to keep signatures aligned with directory data and organizational changes.
Google Workspace: Key Details to Know
- Gmail signatures can be up to 10,000 characters.
- If users include images hosted on Google Drive, those images must have appropriate sharing permissions or recipients will not see them.
- Google explicitly points large organizations toward Marketplace apps if they have many signatures to manage — a strong hint that native controls cover only part of the enterprise use case.
How to Deploy Email Signatures in Microsoft 365
When you need to deploy email signatures organization-wide in Microsoft 365, the primary native path is Exchange mail flow disclaimers.
Option 1: Use Exchange Mail Flow Rules
Admins can create organization-wide signatures in the Exchange Admin Center by navigating to Mail flow > Rules and selecting Apply Disclaimers. You can apply the rule to all outbound mail or target it conditionally, then append or prepend a signature block.
Microsoft supports dynamic variables including %%DisplayName%%, %%Title%%, %%Department%%, %%PhoneNumber%%, and %%Email%%, which provides basic personalization pulled from Azure AD.
Step-by-Step Setup
- Open the Microsoft 365 Admin Center and navigate to Exchange > Mail flow > Rules.
- Click the + icon to create a new rule. Select “Apply disclaimers” as the rule type.
- Name the rule clearly — for example, “Company Email Signature — All Users.”
- Under “Apply this rule if,” select “The sender is located inside the organization.”
- Under “Do the following,” select “Append the disclaimer to the message body” and paste your HTML signature template.
- Insert dynamic variables (%%DisplayName%%, %%Title%%, etc.) where user-specific data should appear.
- Set the fallback action to “Wrap” to ensure the signature is added even if the message format cannot be modified directly.
- Save and test by sending emails from multiple accounts and devices.
Important Microsoft 365 Limitations
The limitations are significant enough that they should influence your architecture:
- Organization-wide signatures cannot be inserted directly under the latest reply or forward — they appear at the bottom of the entire thread.
- Users do not see server-side signatures in their Sent Items folder.
- Rules may skip lines containing variables they cannot populate (if a user’s Azure AD profile is missing Title, for example, that field appears blank or the line is dropped).
- Disclaimer rules need a fallback action when a message cannot be modified, such as when mail is encrypted. The available fallback options are Wrap, Ignore, or Reject.
- HTML rendering is limited — complex layouts, images, and CSS may not render consistently. Images must be hosted externally since transport rules do not support embedded images.
If your stakeholders expect banners, precise placement in reply chains, and sender-visible signatures during compose, native mail flow rules alone may not be sufficient.
What About Outlook Client-Side Signatures?
Microsoft’s Outlook ecosystem has been shifting toward cloud-roamed settings. Starting with Outlook for Microsoft 365 Version 2303 and higher, signatures can sync across devices via the cloud. Admins can disable roaming settings through Group Policy if needed.
For IT admins, the takeaway is straightforward: old-style file-copy methods and local profile tricks are increasingly fragile in a world of roaming settings, multiple Outlook clients, and mixed-device fleets. If you are still relying on login scripts to deploy signatures, plan to modernize.
Third-Party Tools to Deploy Email Signatures Organization-Wide
Third-party tools solve the limitations of native platform options by providing a centralized dashboard for designing, deploying, and managing signatures across both Microsoft 365 and Google Workspace environments.
What to Look For When Evaluating
- Platform support — works with both Microsoft 365 and Google Workspace, handles hybrid environments.
- Design editor — non-technical users can create and update templates without editing raw HTML.
- Dynamic fields — pulls employee data from your directory (Azure AD, Google Directory, or HR systems) automatically.
- Department and role targeting — assigns different signatures to different teams based on group membership or attributes.
- Banner campaigns — adds and rotates promotional banners across all signatures centrally.
- Analytics — tracks banner clicks and measures campaign performance.
- Mobile support — applies signatures server-side so they appear on every device.
Typical Deployment Process
- Connect your email platform (Microsoft 365 or Google Workspace) via OAuth or API integration.
- Sync your user directory to pull names, titles, departments, and phone numbers automatically.
- Design your signature template using the visual editor or import existing HTML.
- Set rules for which users or groups receive which template.
- Deploy to all users with a single action.
- Monitor deployment status and verify signatures are appearing correctly.
This is the context where a platform like BulkSignature fits. BulkSignature provides centralized email signature management for both Google Workspace and Microsoft 365, with directory sync, templates, role-based access, and deployment across devices. The important point is not that every company needs a third-party platform — it is that once requirements expand beyond appending one line to every email, the admin burden rises quickly, and that is when purpose-built tooling becomes easier to justify.
Handling Exceptions When You Deploy Email Signatures Organization-Wide
Exceptions are where most deployments get messy. Executives want richer signatures. Sales wants banners. Legal wants country-specific disclaimers. Support teams use shared mailboxes. New hires need an automatic signature on day one.
Policy Segmentation
The cleanest approach is policy segmentation. Define signature classes by attribute, not by person. For example:
- Standard employee
- Executive leadership (additional credentials, different layout)
- Customer-facing sales (banners, promotional content)
- Regional office (jurisdiction-specific legal text)
- Contractor (limited branding)
- Shared mailbox (department-level signature, no personal details)
Tie those classes to directory groups or user attributes. In Google Workspace, that means separate rules plus API logic. In Microsoft 365, it means different mail flow rules with conditions. In third-party tools, it means template assignment rules mapped to groups.
New Employee Onboarding
When a new employee joins, their email signature should be applied automatically. With transport rules, this happens by default as long as the rule targets all internal senders and the new user’s directory profile is complete. With third-party tools, most platforms sync with your directory on a schedule (typically every 1 to 4 hours) and add new users automatically.
Action item: Ensure your onboarding process includes completing all directory fields (display name, title, department, phone number) before the new hire’s first day. Missing fields result in blank spaces or dropped lines in the signature.
Seasonal and Campaign-Based Updates
Marketing teams frequently want to update signature banners for product launches, events, or seasonal promotions. With transport rules, this requires manually editing the HTML each time — a process that is slow and error-prone. Third-party tools with banner campaign features allow marketing teams to schedule changes independently, without IT involvement.
Pre-Deployment Checklist to Deploy Email Signatures Organization-Wide
Before you deploy email signatures organization-wide, verify the following:
- All user profiles in your directory (Azure AD or Google Directory) have complete information: display name, title, department, phone number, and email.
- Your signature HTML has been tested in Outlook (desktop and web), Gmail, Apple Mail, and at least one mobile client.
- Legal has approved the disclaimer text for all applicable jurisdictions.
- You have a plan for handling exceptions (executives, part-time employees, shared mailboxes).
- You have tested fallback behavior — what happens when a dynamic field is empty.
- You have documented the process so another admin can update signatures when you are unavailable.
- You have communicated the change to employees and set expectations, especially if they previously managed their own signatures.
- You have planned a phased rollout rather than deploying to everyone simultaneously.
Common Pitfalls When You Deploy Email Signatures Organization-Wide
The most common failure is assuming signatures are only a formatting problem. In reality, they are an identity-data problem. Missing titles, inconsistent phone formats, and ungoverned aliases produce broken outputs faster than any template bug.
The second pitfall is testing only new messages. Always validate replies, forwards, mobile mail, shared mailboxes, and encrypted mail paths. Microsoft explicitly documents fallback behavior for messages that cannot be modified — ignoring this leads to unexpected gaps.
The third pitfall is relying on user-hosted assets. In Google Workspace, image visibility fails if sharing is not configured correctly for Drive-hosted images. In Microsoft 365, externally hosted images can break if the hosting service changes URLs or has downtime.
The fourth is over-customizing. Every exception increases operational load. If you can solve 90% of the business need with three templates instead of twelve, do that.
Measuring Success After You Deploy Email Signatures Organization-Wide
A signature rollout is successful when it becomes boring — no one talks about it because it just works. Track these four metrics:
| Metric | What to Measure | How to Check |
|---|---|---|
| Coverage Rate | Percentage of outgoing emails with the correct signature applied | Spot-check by having employees forward test emails to a monitoring mailbox |
| Rendering Accuracy | Signatures display correctly across email clients | Send test emails to Outlook, Gmail, Apple Mail, and Yahoo Mail — compare results |
| Support Ticket Volume | Signature-related tickets after rollout | Track ticket categories in your ITSM tool |
| Data Quality | Signatures with missing title, phone, or department | Audit directory fields; count blank or placeholder values |
If you use a platform with analytics, you can go further and measure template adoption, campaign click-through rates, and change completion times.
Final Takeaway
If your goal is basic enforcement — legal text on every outbound email — native controls in Google Workspace and Microsoft 365 are often enough. If your goal is branded, personalized, cross-platform signatures that adapt to departments, executives, and ongoing organizational change, native controls start to show their limits.
For most IT admins, the best strategy is to start with the operating model: decide what must be enforced, what must be personalized, and what must be delegated. Once that is clear, the right path to deploy email signatures organization-wide becomes much easier to choose.
Frequently Asked Questions
How do I deploy email signatures organization-wide to all users?
You can deploy email signatures organization-wide using Microsoft 365 transport rules, Google Workspace routing rules or the Gmail API, or a third-party management tool. Transport rules work server-side and apply to all outgoing email automatically. Third-party tools add a centralized dashboard for design, targeting, and analytics. The right choice depends on your platform, design requirements, and how often you need to update signatures.
Can I set different email signatures for different departments?
Yes. In Microsoft 365, create multiple transport rules filtered by security group or organizational unit. In Google Workspace, apply different routing rules per OU or use the Gmail API with service accounts. Third-party tools typically offer the most flexible department-based targeting, allowing you to map templates to groups, roles, or locations from a single interface.
Do email signatures deploy to mobile devices?
Server-side signatures — whether from transport rules or a third-party tool using server-side injection — appear on every outgoing email regardless of device. Client-side signatures configured in Outlook or Gmail apps only appear on that specific device. For consistent mobile coverage, server-side deployment is the recommended approach.
What happens to existing signatures when I deploy centrally?
Transport rules append the centralized signature in addition to any client-side signature the user has already configured. This can result in duplicate signatures. Best practice: instruct users to remove their existing client-side signatures before deploying, or use a third-party tool that replaces client-side signatures automatically.
How often should I update email signatures?
Update the signature template whenever branding changes. Employee-specific fields should update automatically through directory sync. Promotional banners should rotate on your marketing calendar — monthly or quarterly is common. Review the legal disclaimer at least annually or whenever regulations change in your industry.





